The Internet has become a part of our lives. We can hardly imagine how we used to live without it. In recent years, we can observe a very dynamic development of the Internet and its services. We communicate on social networks, make purchases online, and attend online presentations and webinars. We practically exist online. But often we forget about the security and privacy of data on the Web. But we live in times when data is expensive. Therefore, most companies try to collect the information about us, about our habits, about what we love, what we eat and what we want to buy.
Keeping secrets was pretty easy once. You just didn’t share your info. In our time, desire alone is not enough. Information that we don’t want to tell anyone is collected by our browsers on PCs and mobile devices. Therefore, you should take care of online privacy yourself. Do not click on suspicious links, download VPN, and also use encryption and strong passwords. Today I will talk about the simplest security methods that will help ensure the safety of your personal data on the Web.
Use encryption in messengers
We often communicate on social networks and various messengers. We talk about personal life events, discuss work issues, exchange information, including email, phone numbers or other data. But it is not always safe. The data that we send through the messenger is extremely easy to intercept, and hackers know it.

Encryption is an effective way to protect sensitive data. It should be used not only for data protection, but also during personal text conversations. All you have to do is use an encrypted messenger such as Signal, Viber, Telegram and others. If the manager has no way to encrypt data, you shouldn’t use it.
Be careful when clicking on links and opening documents
Human carelessness and negligence are often the cause of viruses. Of course, this leads not only to malfunctions of smartphones and laptops, but also to the loss of personal data.
Online privacy can be obtained not only with the help of tools that will protect your data when browsing websites. If we want to be safe on the network, we must also protect our email first. It doesn’t matter if you use it for personal purposes or if it is a corporate adress.
Bank customers very often become victims of email attacks. Hackers imitate our banks, and opening their message or attachment to it can lead to serious consequences. You can easily lose all your money that way. The same goes for personal or corporate data, so be very careful when opening links or attachments.
Protect your computer’s drive
On the hard drive of a home or work laptop we store not only our photos and personal data, but also work-related files. We want them to be secure and protected – and accessed only by the people with clearance. Therefore, the hard drive of your computer also requires some protection.
Windows 10 Professional users can use the built-in Bitlocker encryption feature. It is quite simple and intuitive to configure and use. Just a couple of minutes is enough to enable this function and start using it. With Bitlocker, your data will definitely be protected. Now access to your laptop disk will be encrypted. You’ll be able to access the device only by entering a specific password or using a USB key. There are third-party hard drive encryption tools that are available on the Web, but Bitlocker is already on your operating system.
Avoid weak passwords
One of the easiest things you can do to protect your data on the Internet is use strong passwords and use them wisely. You must have a separate password for each site.

A good password is not hard to come up with. One that consists of only letters or numbers is much easier to crack than one that also contains special characters. Complicate your passwords as much as possible. However, do not use one password everywhere, because when a hacker breaks it, he will gain access to all your services.
Read also: 5 simple tips: How to create and manage passwords
In order not to get lost among many passwords, it is worth using special password managers such as Last Pass or KeePass and others.
Make use of two-factor authentication
Often one password is not enough to protect yourself from hacking or hacker attacks. Almost all self-respecting and customer-friendly services have long introduced two-factor authentication. You can also protect your data not only with a password, but, for example, with a special code that will be sent by text message. With this authorization scheme, stealing your personal data is more difficult.

Here we add that due to two-factor authentication, someone who tries to access our data will encounter an insurmountable obstacle – the need to physically obtain our phone. This method should be used for email, social or work accounts.
Use secure https protocol
It is recommended to use sites with secure https protocol. This is a special extension of the http protocol that is used for SSL encryption and secure data exchange between the site and yourself. In other words, it means that the site has passed a certain reliability check, having received a certificate that contains all the information about it and its owner.

Of course, attackers do not burden themselves with obtaining a certificate for their site. You need to be very careful when opening certain sites without the https protocol. Not only are they dangerous for your device, but they can also steal your data.
But constantly checking whether the site uses a protocol or not can be tiresome. Do not fret: just use the HTTPS Everywhere extension for your browser, and it will check the HTTPS connection for you, as well as provide an encrypted connection on each site. This add-on is available for Chrome, Firefox, and Opera for PC and Android.
Besides add-on, it is sensible to go with paid SSL cert as there are low cost or cheap SSL certificates available in SSL industry. You can select any SSL from a portfolio of SSL providers and if you have no know-how of which one to choose, you can ask the provider for better suggestions.
Use VPN
VPN technology creates a virtual tunnel that protects the data passing through it. When you use a VPN service, anyone who wants to see what we are doing will be disappointed: all a hacker will see is the fact that the data is being transferred. However, it is impossible to see what is happening inside this virtual tunnel.

I am sure that most of you are familiar with the capabilities of VPN services. But they not only provide an opportunity to access restricted and blacklisted sites, social networks or resources, but also help protect our personal data. This tool will be especially useful if you often use public Wi-Fi. Thanks to the VPN connection, the transmitted data is almost impossible to intercept inside the local network.
Remember that incognito mode is not completely private
Incognito mode is one of the easiest ways to achieve privacy. It is accessible from almost any browser. Unfortunately, private mode also has some limitations. It will not help us become completely invisible and will not protect us from tracking.
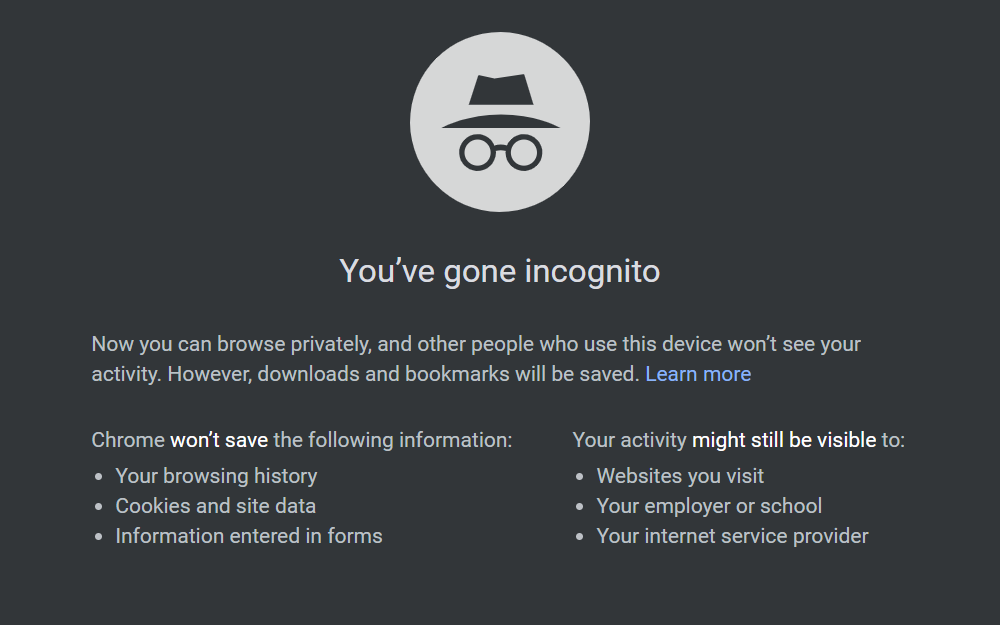
When using a normal browser in incognito mode, it is worth remembering that the data on the visited resources can be tracked by the administrator of the local network or your Internet provider. Incognito mode does not protect your privacy, it just does not show the exact location and does not save the browser history. However, the amount of personal data that may become available to websites will be reduced.
For enhanced privacy on the Web, you should use special browsers such as Tor Browser. Using the onion network allows you to maximize your privacy on the Internet, although it also does not mean 100% guarantee of security.
Use safe search engines
Google search engine is the best and most popular, sure, but on the other hand, it is one of the most “leaky” search engines out there. It just oozes personal data.
However, we can use an alternative in the form of DuckDuckGo, which provides anonymity on the Web. This is a relatively unpopular search engine, but it certainly deserves our attention, as more and more people are interested in online privacy. DuckDuckGo does not store cookies, IP addresses and does not bombard the user with ads.
But you need to understand that Google’s personal search results are more accurate thanks to the data they collect about us.
Verdict
Although there are no ways to guarantee absolute security of your personal data, the implementation of at least a few of the tips described above will significantly increase the level of data security and protect you from the most common types of cyber attacks. And remember, everything depends on you and your diligence.